 Recently, we took some time to peruse the U.S. patents that have been issued to IBM in recent weeks, finding some intriguing developments in virtual world and eBook development. Today, we’re moving over to the other side of this corporation’s intellectual property activities to profile the patent applications filed by IBM in recent months with the U.S. Patent and Trademark Office.
Recently, we took some time to peruse the U.S. patents that have been issued to IBM in recent weeks, finding some intriguing developments in virtual world and eBook development. Today, we’re moving over to the other side of this corporation’s intellectual property activities to profile the patent applications filed by IBM in recent months with the U.S. Patent and Trademark Office.
As we noted in that previously published piece, IBM enjoys an incredibly strong patent portfolio relative to the amount of money that it invests into research and development. Some of this increased patenting activity is supported by IBM programs that enable systems administrators and those in other non-traditional R&D positions to participate in the process of developing innovations and filing patent applications. IBM is looking to invest $40 billion by 2018 in its data, cloud, security and mobile & social businesses, which is likely where much of the company’s IP portfolio will continue to focus in the coming months and years.
Many of the technologies developed by IBM are often licensed for use in computing devices and electronics that are manufactured by other companies. For example, an IBM innovation for software security that wraps applications into malware-proof containers has been incorporated into a BlackBerry tablet device being developed for government and corporate clients. IBM also creates software 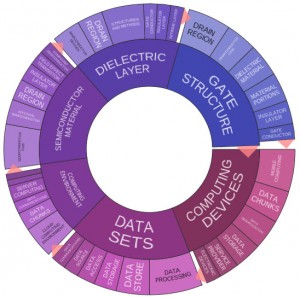 solutions to address issues being encountered by other high tech firms. In early March, IBM’s X-Force Application Security Research Team announced that it worked with both Android and Dropbox to develop a security patch fixing a vulnerability that could allow the injection of malicious data into third-party apps via cyber attack.
solutions to address issues being encountered by other high tech firms. In early March, IBM’s X-Force Application Security Research Team announced that it worked with both Android and Dropbox to develop a security patch fixing a vulnerability that could allow the injection of malicious data into third-party apps via cyber attack.
Not only do the Innography patent research tools that we use during our Companies We Follow series help us more thoroughly investigate patent portfolios, we can also get a sense of the kind of patent applications being filed by a company. Over the previous three months, this corporation has filed a total of 1,790 patent applications with the USPTO in that time. As the text cluster posted here will show our readers, IBM has been busy developing inventions related to computing devices and environments as well as semiconductor materials and data sets, especially data storage.
[Companies-1]
Financial Developments from IBM Combat Fraud, Improve Pricing Activities
Interestingly, we noted a great number of innovations filed by IBM that extend into the field of financial services. The company has already been working to develop Bitcoin-style systems, especially the “blockchain” digital currency transaction list supporting Bitcoin, that are capable of serving as digital cash and payment mechanisms for major currencies.
A business’s front office in a variety of industries will be able to more effectively set pricing strategies for its products thanks to the technology outlined within U.S. Patent Application No. 20150066956, entitled Behavior Pricing Analytics. The patent application claims a method for systematically determining a pricing strategy by receiving historic transaction data for a good or service and determining a possibility that a customer chooses an alternative good or service given the historic transaction data and the customer’s perception of deal being offered with the alternative good or service. This innovation incorporates the use of behavioral models in order to determine more effective pricing strategies in such a way that accounts for the thrill that a consumer can feel when accepting a deal offered by a competitor. Real-time financial data analytics supporting improved sales and payments are at the center of U.S. Patent Application No. 20150073902, which is titled Financial Transaction Analytics. The method claimed here involves generating a customer profile including multiple commercial-related parameters based upon past customer transaction data, determining a merchant’s identity from a customer transaction message, determining customer location information from the message and generating at least one personalized commercial offer for the customer. This system increases the capacity of a business to offer location-specific offers to customers directly through an SMS text message.
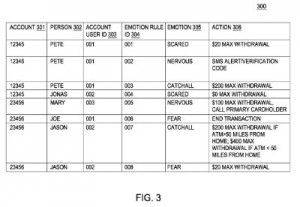 IBM is also getting involved in the fight against fraud enabled by cybersecurity risks which are endemic to the financial industry, a topic we’ve been writing about heavily in recent days. Increased security measures for bank cards associated with debit accounts are the focus of U.S. Patent Application No. 20150066764, entitled Multi Factor Authentication Rule-Based Intelligent Bank Cards. The system claimed here includes one or more computer processors to execute a program that receives valid authentication information for a card associated with an account, verifying that a captured image of a person presenting the card matches an authorized user image, analyzing the captured image to detect an emotion of the person and controlling access to the account based on the determination that the detected emotion satisfies an emotion rule associated with the account. This system could restrict access to an account if it determines that a user is experiencing a nervous or agitated emotional state, which could indicate suspicious behavior.
IBM is also getting involved in the fight against fraud enabled by cybersecurity risks which are endemic to the financial industry, a topic we’ve been writing about heavily in recent days. Increased security measures for bank cards associated with debit accounts are the focus of U.S. Patent Application No. 20150066764, entitled Multi Factor Authentication Rule-Based Intelligent Bank Cards. The system claimed here includes one or more computer processors to execute a program that receives valid authentication information for a card associated with an account, verifying that a captured image of a person presenting the card matches an authorized user image, analyzing the captured image to detect an emotion of the person and controlling access to the account based on the determination that the detected emotion satisfies an emotion rule associated with the account. This system could restrict access to an account if it determines that a user is experiencing a nervous or agitated emotional state, which could indicate suspicious behavior.
Innovations for Preventing Malicious Fraud and Information Through Digital Networks
As we’ve noted in a lot of our recent coverage of cybersecurity risks in our increasingly digital world, ensuring that parties interacting through digital networks are all operating in good faith is increasingly important for keeping business moving. We noted at least one IBM innovation in this field reflected in the recently published U.S. Patent Application No. 20150074395, which is titled Establishing a Trust Relationship Between Two Product Systems. The patent application would protect a method for establishing a trust relationship between two products by receiving a registration request from an application device to access a resource on a resource device, sending a registration response, which includes an authorization code and a symmetric key, through the use of a redirection uniform resource identifier (URI), receiving an access token request at the resource device which includes the symmetric key, authorization data and URI and sending an access token to the application device to establish a trust relationship between both the resource and the application device. This innovation provides a more robust system for preventing unauthorized product use in situations where multiple products utilize a common user registry or common user authentication credentials.
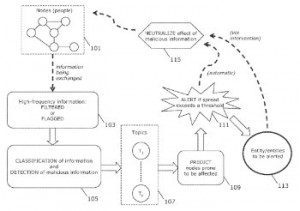 IBM has also developed an intriguing tool for ensuring that incorrect information isn’t improperly disseminated through digital networks, where it could be accepted as truth by unwitting users. U.S. Patent Application No. 20150067849, which is titled Neutralizing Propagation of Malicious Information, claims a method of controlling a spread of malicious information in a network by utilizing at least one processor to track a viral spread of information in a network comprising interconnected nodes, identifying malicious information in the viral spread, predicting a topic-specific sub-network of nodes prone to be affected by the malicious information and neutralizing the effect of the malicious information at the sub-network of nodes. This invention enables a quick response for neutralizing malicious rumors about destructive events or natural disasters before they can spread through a large network.
IBM has also developed an intriguing tool for ensuring that incorrect information isn’t improperly disseminated through digital networks, where it could be accepted as truth by unwitting users. U.S. Patent Application No. 20150067849, which is titled Neutralizing Propagation of Malicious Information, claims a method of controlling a spread of malicious information in a network by utilizing at least one processor to track a viral spread of information in a network comprising interconnected nodes, identifying malicious information in the viral spread, predicting a topic-specific sub-network of nodes prone to be affected by the malicious information and neutralizing the effect of the malicious information at the sub-network of nodes. This invention enables a quick response for neutralizing malicious rumors about destructive events or natural disasters before they can spread through a large network.

![[IPWatchdog Logo]](https://ipwatchdog.com/wp-content/themes/IPWatchdog%20-%202023/assets/images/temp/logo-small@2x.png)

![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2024/04/Patent-Litigation-Masters-2024-sidebar-early-bird-ends-Apr-21-last-chance-700x500-1.jpg)

![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/WEBINAR-336-x-280-px.png)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/2021-Patent-Practice-on-Demand-recorded-Feb-2021-336-x-280.jpg)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/Ad-4-The-Invent-Patent-System™.png)






Join the Discussion
One comment so far.