“Given the legal questions around the patentability of software and computing technology, tech companies have found it hard to project the proper approach for patenting these types of technologies. This confusion is likely to apply to quantum computing.”
 Quantum computing continues to gain traction as an emerging technology, with potentially far-reaching and dangerous applications in the United States and worldwide. However, there are some applications for the technology which have not yet passed theoretical muster. In other words, the case for quantum advantage cannot be made by reference to known mathematical algorithms. But many applications, including quantum decryption (discussed below), have been concretely mapped out on a theoretical level and are now subject to only “engineering limitations” (i.e., implementation details).
Quantum computing continues to gain traction as an emerging technology, with potentially far-reaching and dangerous applications in the United States and worldwide. However, there are some applications for the technology which have not yet passed theoretical muster. In other words, the case for quantum advantage cannot be made by reference to known mathematical algorithms. But many applications, including quantum decryption (discussed below), have been concretely mapped out on a theoretical level and are now subject to only “engineering limitations” (i.e., implementation details).
Typically, when technology reaches this stage in the cycle of innovation, the patenting in such spaces becomes relatively “hot.” The idea is that when a problem has a fixed solution, human ingenuity will prevail in actuating such a solution. While there are solid reasons for believing that quantum computing is one of the hardest things to implement within reach of inventive thought, it is hard to bet against humanity ultimately conquering it.
Investors, regulators, and industry players can better project the trajectory and timeline of disruptive technologies once they have reached the implementation stage. And to a varying extent, they have a prediction as to the scope of the market. However, it can be even harder to project how the legal landscape will evolve for such technology, or whether and to what extent the legal rewards and barriers will facilitate a broad or narrow landscape of economically viable competitors. Some believe that in the United States, quantum computing will be a vibrant and central technological industry, similar to what digital computing (commonly referred to in the quantum computing industry as “classical computing”) is today. Others have observed the relative difficulty and limited applicability of such complicated technology and foresee a narrower “winner takes all” scenario.
The Technological Background of Quantum Cryptography
The theoretical framework for quantum decryption, popularly referred to as “Shor’s Algorithm,” has become widely accepted as scientifically correct by the academic community. So, there is a fear among many governmental players that it is only a matter of time before the United States or one of its adversaries will deploy quantum decryption to intercept secure, highly sensitive data. Fred Guterl described one of the United States government’s most acute concerns in his 2019 article, Are We Ready For a “Quantum Surprise” From China?:
The nightmare scenario, from the standpoint of U.S. national security, is that China develops a working quantum computer without tipping its hand.
Governmental Response
Because of the unique national security concerns raised by the likely advent of quantum decryption in the mid-to-near-term future, the United States and other countries’ governments have been closely watching the development of this technology in their jurisdictions and abroad. However, quantum computing also promises to bring about many commercial applications. Such applications include random number generation, advanced seismology, and groundbreaking medical simulations. For this reason, pundits have labeled quantum computing a “dual-use” technology.
Because of the imminence of quantum decryption, the government and private industry players have a significant, investment-backed interest in developing encryption techniques that protect data against quantum decryption. Experts refer to these techniques as quantum-safe encryption or post-quantum encryption (PQE).
Note: One limitation of quantum-safe encryption is that nefarious entities can currently collect information encrypted based on known cryptographic standards such as prime factorization and later decrypt the data when quantum decryption becomes available.
There is a strong economic incentive for both the government and private entities to develop and adopt quantum encryption standards to protect precious or sensitive data.
Offensive and Defensive Consideration
So, when we look at the patenting and industrial landscape of quantum cryptography, it is essential to note the bifurcation of technological development between “offensive” (decryption) and “defensive” (encryption) developments. Moreover, in recent innovation cycles for emerging technologies, for example, computer vision, there has been an imbalance in innovation between the offensive and defensive sides of the coin. For instance, tech companies have been more eager to invest in deployable dual-use applications, like facial imaging and “fingerprinting,” than in the defenses against such applications. These imbalances can lead to impediments to national security, innovation, and unique legal challenges. Therefore, it is crucial to consider the incentivization strategy for each aspect of quantum cryptography, with an eye to what may catalyze these types of imbalances to address them earlier in the innovation cycle.
For instance, the patentability questions for quantum computer systems generally based on the abstract idea exception under 35 U.S.C. § 101 as set forth by Alice Corp. v. C.L.S. Bank (discussed below) are likely to be significantly different than those for quantum-safe encryption techniques. Similarly, the concern that patents will create an impenetrable barrier to mass adoption is more acute for encryption techniques. Adopting a patented standard will lead to questions of who in the supply chain must license the standard.
Given this technological landscape, what are the best policies for the United States to take regarding the patenting of these related technologies? While this article does not seek to discover the answer to this challenging question, it will discuss the current approaches that the industry has taken and the potential patent-related issues that lie ahead for quantum cryptography.
Quantum-Safe Encryption
Ironically, the response to a technological capability that does not yet exist (quantum decryption) has preceded it in importance. The National Industry of Standards and Technology (NIST) plans to release the initial standard in 2022, long before most stakeholders expect quantum computing to have practical applicability (although our knowledge of the global quantum computing landscape may be limited).
One way of preventing adversaries from attacking us with quantum capabilities is by preventing the international transfer of necessary components to those countries. The United States will most likely subject the exportation of quantum dilution refrigerators to China to unique controls. These refrigerators are essential components of virtually all known quantum computer implementations. As it stands, the United States may be required to do so unilaterally.
Classical Cryptography
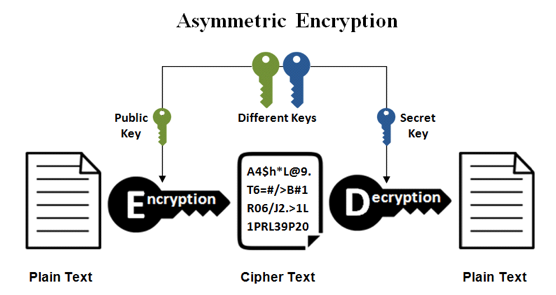
While quantum computers are incredibly novel and have the potential to do things that a classical computer could never do, we can learn from the development of current cryptographic standards. For example, upon the advent of computers came the need to secure confidential communications. Early on, “symmetric” encryption came about as an obvious solution. If both the sender and the recipient knew the password or cipher, they could access the information. But what if the sender and recipient have never communicated and can only communicate through an insecure channel? The answer is “asymmetric encryption” (or “public-key encryption” (PKE))—where there are two parts of the key.
As classical computers developed, there was an increasing need for PKE, and scientists and engineers wrestled with its implementation. The idea of PKE is to make the public key extremely hard to reverse engineer. It usually requires changing the key over time because it can always theoretically be reverse engineered in enough time. Further, even when the time necessary for reversing a public key seems impractical to achieve, there are still ways to accurately guess parts of the public key or the cipher of the encrypted message without access to the entire key.
While the true technical complexity of PKE can be confusing, the important takeaway for this discussion is that it is pretty tricky and required extensive research and development (R&D) before society achieved acceptable performance levels from PKE systems. And like many areas that undergo extensive R&D, patents resulted and played a role in technological innovation.
The “Pioneer Patents”
When tyrants die, the people parade with the head on a stick; when loved ones pass on in Ireland, the families celebrate a life well-lived; but when patents expire, they often slip away into the night.
Peter Wayner, A Patent Falls, and the Internet Dances
Two groups secured patent rights related to these innovations, which would eventually be referred to as the “pioneer patents” in Greg Vetter’s Patenting Cryptographic Technology. A professor led one group at Stanford, Martin E. Hellman, and his group of graduate students. Hellman’s group developed two patents: (1) the Diffie-Hellman patent (U.S. Pat. No. 4,200,770), and (2) the Hellman-Merkle patent (U.S. Pat. No. 4,218,582). Following on from the Stanford patents, a trio of professors from MIT developed the RSA patent (U.S. Pat. No. 4,405,829). IBM also developed its Data Encryption Standard (DES) (U.S. Pat. No. 3,962.539), which became popular, used explicitly by the United States government for over two decades.
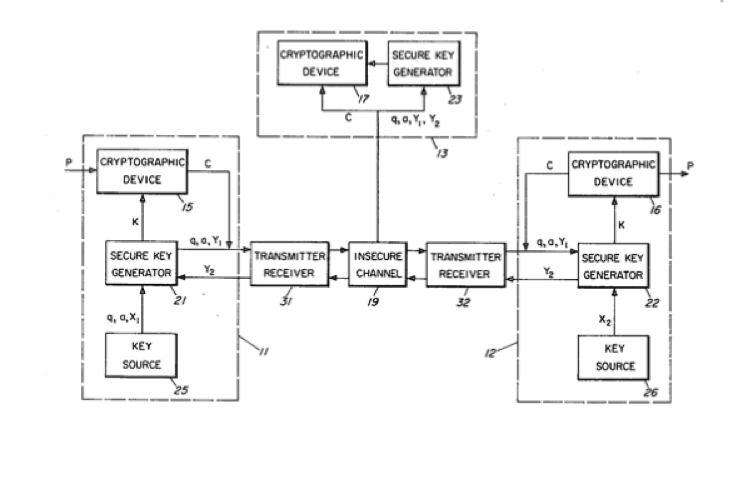 Figure 1 of the Diffie-Hellman patent
Figure 1 of the Diffie-Hellman patent
The “pioneer patent” owners faced significant pushback when leveraging their exclusive rights to these cryptographic innovations. For instance, when the federal government adopted the DES standard, there was confusion about whether all vendors servicing the government needed to license IBM’s patented standard. As a result, the government ultimately issued royalty-free licenses to these third-party vendors, as noted in the Federal Information Processing Standards (FIPS) publication 46-3.
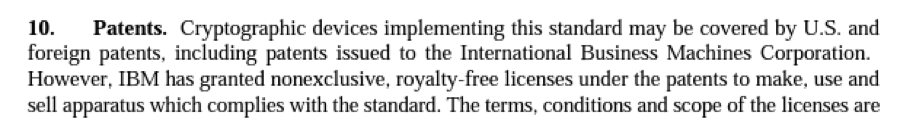 Federal Information Processing Standards (FIPS) Publication 46-3, Section 10
Federal Information Processing Standards (FIPS) Publication 46-3, Section 10
Unlike the DES patent, the other pioneer patents were not subject to this royalty-free patent licensing scheme, and there was litigation over the patents. While the atmosphere surrounding these raised significant concerns about exclusive rights hampering the industry’s growth, it also created a rich market for follow-on inventions.
NIST’s Patent Waiver
The National Quantum Initiative Act in 2018 entrusted NIST with the responsibility of allocating up to $80 million per year to further the Act’s goals between 2019 and 2033. As a result, NIST hosts and takes part in many efforts to increase the capabilities of quantum information systems (QIS) in general.
One way that NIST promotes the progress of (QIS) is by hosting a “competition” to develop the initial standard of Post-Quantum Encryption (PQE). NIST’s process for evaluating post-quantum encryption techniques includes a detailed set of Submission Requirements. As part of these Submission Requirements, NIST makes participants declare that they will not assert patent rights related to their encryption standards. Still, several candidates in the running have not yet signed the waiver, and NIST is still considering how to handle that situation.
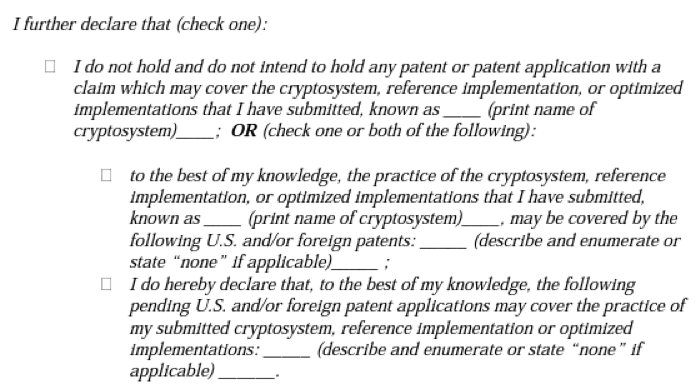 Submission Requirements and Evaluation Criteria for the Post-Quantum Cryptography Standardization Process, p. 10
Submission Requirements and Evaluation Criteria for the Post-Quantum Cryptography Standardization Process, p. 10
Given NIST’s essential role in the standards-development for PQE, there is pressure to strike the right balance with the IP system on this issue. And whether NIST decides to support a standard subject to a patent most likely requires consideration of the pioneer patents and their effect on innovation.
The Patentability of Algorithms under Alice
There are political reasons why leveraging a patent for an inventive encryption technique may be difficult, but legal challenges exist. In 2013, the Supreme Court decided Alice v. C.L.S. Bank solidified a sea-change in the patentability of software, which is often subject to the “abstract idea” exception under 35 U.S.C. § 101.
The questions for cryptography patents are well-illustrated by a recent case, Dropbox, Inc., Orcinus Holdings, LLC, v. Synchronoss Technologies, Inc., decided June 19, 2020, by the United States Court of Appeals for the Federal Circuit (CAFC). Interestingly, the CAFC at oral argument observed technical parallels between the patent’s method steps and the physical act of using different key cards to offices at a government agency. However, it seemingly ignored the claims’ actual substance, eliminating unnecessary authentication filters along a file access path a given user.
It is often possible to envision a possible analog or “brick and mortar” parallel to these patented encryption techniques by eliminating the general-purpose computing components from the elements of the claim. But a better approach may be to ask whether such an approach is feasible and valuable without those digital components.
Quantum Decryption: Is Quantum Computing an Abstract Idea under 35 U.S.C. § 101?
The patentability of quantum decryption systems turns on whether “general purpose” quantum computing will be treated the same way by the courts as have inventions implemented on “general purpose” computers. Realistically, we can think of this question in terms of substantive law or practical reality.
In terms of practical reality, the USPTO and the courts have shown a tendency to decide these questions based on the public interest and possibly “technical merit”—that is, the ability to describe inventions in terms of “hard tech rather than pure software.” In addition, there are empirical studies that show that patent applications filed in the United States that sound in “hard tech” are more likely to avoid the snare of 35 U.S.C. § 101.
However, the current landscape appears to be unsustainable and potentially volatile. As a result, there are resounding calls for reform to the legal landscape in the United States. Recently, the USPTO released a call for comments addressing how the Office should respond to the confusion resulting from recent case law and patent prosecution outcomes. The CAFC, for instance, has been invalidating granted patents challenged under the abstract idea exception at a rate of greater than 80% and is continuing to hear more of these cases every year.
Given the legal questions around the patentability of software and computing technology, tech companies have found it hard to project the proper approach for patenting these types of technologies. This confusion is likely to apply to quantum computing. Critically, the relative “technical merit” of these quantum computing inventions facilitate their allowance at the USPTO, but in 10-15 years, when litigation ripens for the same patents, will the same designs appear generic given the projected future landscape of the technology?
It’s Our Ball
While it is difficult to envision the appropriate balance for this new cycle of quantum computing innovation, it has become clear that several of our global adversaries, including China, have been patenting quantum computing technology at a rapid and ever-intensifying rate. Thus, it appears the ball is now in our court to address these difficult questions and attempt to define our view of patenting in each of the discussed innovation areas.
Image Source: Deposit Photos
Copyright: Elnur_
Image ID: 239228752

![[IPWatchdog Logo]](https://ipwatchdog.com/wp-content/themes/IPWatchdog%20-%202023/assets/images/temp/logo-small@2x.png)

![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2024/04/Patent-Litigation-Masters-2024-sidebar-early-bird-ends-Apr-21-last-chance-700x500-1.jpg)

![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/WEBINAR-336-x-280-px.png)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/2021-Patent-Practice-on-Demand-recorded-Feb-2021-336-x-280.jpg)
![[Advertisement]](https://ipwatchdog.com/wp-content/uploads/2021/12/Ad-4-The-Invent-Patent-System™.png)







Join the Discussion
11 comments so far.
Anon
September 13, 2021 09:57 amPeter’s post at 9 should be bookmarked, as it provides a substantive background to the oft used phrase that the “soft” in software is merely ONE of many design choices in the computing arts, and is entirely patent-equivalent to the other design choices (specifically, hardware).
Peter Lablans
August 31, 2021 04:57 pm@6 “Quantum computers are more akin to [old] analog computers, both have an intrinsic mapping between the hardware and the equations solved.”
So do digital computers. Ultimately any operation in digital computers is a switching operation. That many computer operations can be and are represented as mathematical expressions does not change the fact that for each digital computer operation related to that mathematical expression there is an underlying physical circuit.
In that sense a “transfer function” of a circuit or its time-domain equivalent as in analog computers is not different from a specific configuration established by micro-instructions for an ALU.
An operational “quantum computer” to attack encryption or to perform encryption is currently an abstract idea, because it doesn’t exist. It only exists in the mind of people who are working on it. In the thinking of the CAFC a quantum computer may become again abstract after it is realized, because it performs “abstract” operations. Thus no patentable innovation in computer applications is possible.
Not unlike a photographic camera, which was absolutely an abstract idea prior to 1825. The idea was known (in the camera obscura) prior to 1825, the technology was not. Then in 2021 in Yu v. Apple a camera was deemed to be abstract again (“the abstract idea of taking two pictures”).
Physical science has little to do with determination of what constitutes an abstract idea and patent eligibility in the CAFC, it seems.
Theodore Rand
August 31, 2021 02:52 pm@Daniel Alecu,
Additionally, I appreciate your points about true quantum-based encryption techniques and would love to learn more about them if you have links or references to helpful literature on the topic.
Theodore Rand
August 31, 2021 01:50 pm@Daniel Alecu,
I’m happy to debate and discuss the issues discussed in the article. But I do not understand how your most recent comments address my question about your previous comment. Can you respond to my question about the flawed physics fundamentals relating to conservation of energy?
To be clear, post-quantum encryption in the context of this article includes encryption on classical computers that is less vulnerable to decryption by quantum computers. I do not believe there is a need to further distinguish the terminology at this point I’m the development of the technology, and don’t believe it would be helpful to depart from the terminology commonly used in the industry.
While I do not fundamentally disagree with your points about quantum computers and related algorithms being different than digital counterparts, the abstract idea exception is a specific legal doctrine in U.S. patent law that is being consistently being applied to quantum computing patent applications regardless of the technological differences.
Thank you for your feedback.
Daniel Alecu
August 31, 2021 10:56 amDear Theodore,
The quantum encryption relies on a phenomenon called “entanglement”. Two particles are emitted, one for each computer in conversation. There is no way to predict the spin of the two particles but there will be relationship between the two, i.e. both computers-receivers will read the same thing although could be either up or down spin. Any interference will break the entanglement thus the communication. While the two receivers are statistically dependent, for the outside world the encryption is purely random. There is a slight difference between quantum computing and communication based on quantum encryption. Classical encryption based on quantum computing is still vulnerable to attacks, in particular by using quantum computing.
Maybe we should make some distinction ? Quantum computing for classical encryption versus quantum encryption.
Quantum computers are more akin to [old] analog computers, both have an intrinsic mapping between the hardware and the equations solved. So, quantum algorithms (analog computers algorithms as well) are anything but abstract ideas, concrete h/w producing pulses, voltages, currents (that we interpret as abstract ideas).
The “conflation” is an example of on going absurdities. My assumption was you targeted debated not bias confirmation.
Theodore Rand
August 30, 2021 12:58 pm@Daniel Alecu which aspect of the article are you referring to with respect to ignoring fundamental physics? And why are you conflating the concepts discussed in the article with perpetual motion machines?
I did not mean to state anything in this article supporting perpetuum mobile, or otherwise rebutting the second law of thermodynamics.
Thanks.
Daniel Alecu
August 30, 2021 10:56 amThe article neglects fundamental physics and becomes a pure speculation. The UPSTO still allows patents that don’t conserve momentum but block patents that don’t conserve energy (perpetuum mobile). One may know that the energy conservation is a theorem consequence of momentum conservation, which is a nature law (consequence in a way of a fundamental symmetry).
Anon
August 30, 2021 09:05 amWill the author integrate the most recent (and awful) precedential decision of Universal v Apple (see http://www.cafc.uscourts.gov/sites/default/files/opinions-orders/20-2044.OPINION.8-26-2021_1825267.pdf ) into the discussion above?
Peter Lablans
August 29, 2021 09:13 pmNice and timely article. The following relates to additional aspects of patent eligibility of post quantum cryptography.
Quantum Computers are very good at running Shor’s algorithm with regard to Diffie Hellman DH (the discrete logarithm problem) and RSA (the factorization problem). DH basically says that a computation modulo-p of (g^a)^b=(g^b)^a=g^ab and RSA that (m^e)^d=m. Post-quantum (PQ) cryptography as in the NIST PQ competition is focused on cryptographic methods that are insensitive to Shor attacks. The proposed PQ methods (such as Isogenies, Multi-variate, NTRU, McEliece, Learning with errors or LWE methods) do not depend themselves on quantum computing and are in that sense all very classical computer based methods.
One difference of these novel methods with the known ones such as elliptic curve signatures, RSA, ECDH and methods like the Advanced Encryption Standard (AES) and SHA-2 and SHA-3 is that the required level of mathematics to follow the specification of these methods is much higher than the current ones. Reading of the FIPS AES or SHA-2 standard requires some attention for sure. But reading the SIKE/SIDH specification on isogeny based Diffie Hellman or even the Classic McEliece proposal is a whole different ball of wax. This by itself may be a red flag for suits before the Courts.
These novel cryptographic methods are still computer instruction based methods. They pertain to computer operations and cannot be performed ever by humans in their mind or with paper and pencil in the life-time of our universe. These methods generate data-elements that are publicly transmitted and even if you can intercept these data and you know the basics of the instructions, you still cannot decrypt the message or find its related private key, not with any amount of paper and pencil and all the time in the world.
The methods are evaluated by NIST based on their physical usability which indicate their non-abstract nature. That is: these methods are designed based on novel computer functionality (instructions) that generate a message (a public key or signature) of limited length (as to not exceed bandwidth demand) and in a limited processing time that can be handled by current generation processors. These novel methods improve the functionality of the computer. (a complaint often in CAFC opinions is that certain patents in cryptography do not provide any “new” functionality). And these proposed methods are generally not routine, conventional and well understood.
For the Internet infrastructure to continue working safely under potential quantum attacks new computer cryptographic functionality is required. Rather than focusing on the description of the proposed methods (which is very mathematical, extremely so even) one may articulate the problem as a computationally physical one: a set of novel computer instructions is required to generate a message of limited length within a limited processing effort. Many novel sets of instructions could do the job. However, because two machines are involved these instructions have to comply with much more demanding rules of corresponding operations. Hence the need for a more narrowly defined set of instructions which may be called a cryptographic method or primitive and which may be described mathematically. But novel computer functionality it is.
My own inventions go a step further: they modify computer operations that are for instance standard instruction sets (like modulo-n operations in an ALU.) This creates customized and unbreakable classical or PQ cryptographic methods, for which I pursue and have obtained patents. I found Examiners generally willing to be convinced of the patent eligibility of my inventions. Example 41 in Director Iancu’s Memo of Patent Eligibility has been very helpful. (it is based on the original RSA patent). I am less hopeful as it relates to the CAFC. That is why articles like this one are important. This all relates to very useful innovation where our patent system should promote America’s inventors, not hinder or stop them.
Easwaran
August 29, 2021 06:19 pmVery nice article!